Introduction
Maintaining legacy military equipment, telecommunications infrastructure, and long-lifecycle industrial systems creates a critical challenge: sourcing obsolete electronic components that manufacturers discontinued years ago. When a radar system designed in 2005 needs repair in 2025, finding authentic replacement parts becomes essential to mission success.
The stakes are high: system failures, mission delays, compromised safety, and national security risks. According to the Senate Armed Services Committee, approximately 15% of spare and replacement parts purchased by the Pentagon are estimated to be counterfeit. Suspect parts have been discovered in critical platforms including Navy helicopters, Air Force aircraft, and missile defense systems.
For manufacturers and defense contractors, the question isn't whether obsolescence will impact operations. It's how prepared you are when it does.
TL;DR
- Obsolete parts are discontinued components still required for legacy systems operating 20-40 years beyond typical lifecycles
- Counterfeits pose systemic risk—detection requires electrical testing at full operational parameters
- Successful sourcing requires layered strategies: authorized distributors, OEM surplus programs, and specialized aftermarket channels
- Rigorous verification through SAE AS6171 standards is mandatory for non-authorized channels
Understanding Obsolete Electronic Parts
Obsolete electronic parts are components that manufacturers have discontinued but remain essential for maintaining, repairing, or producing existing systems. Unlike end-of-life consumer products, these components aren't obsolete because they failed—they're obsolete because manufacturers moved on.
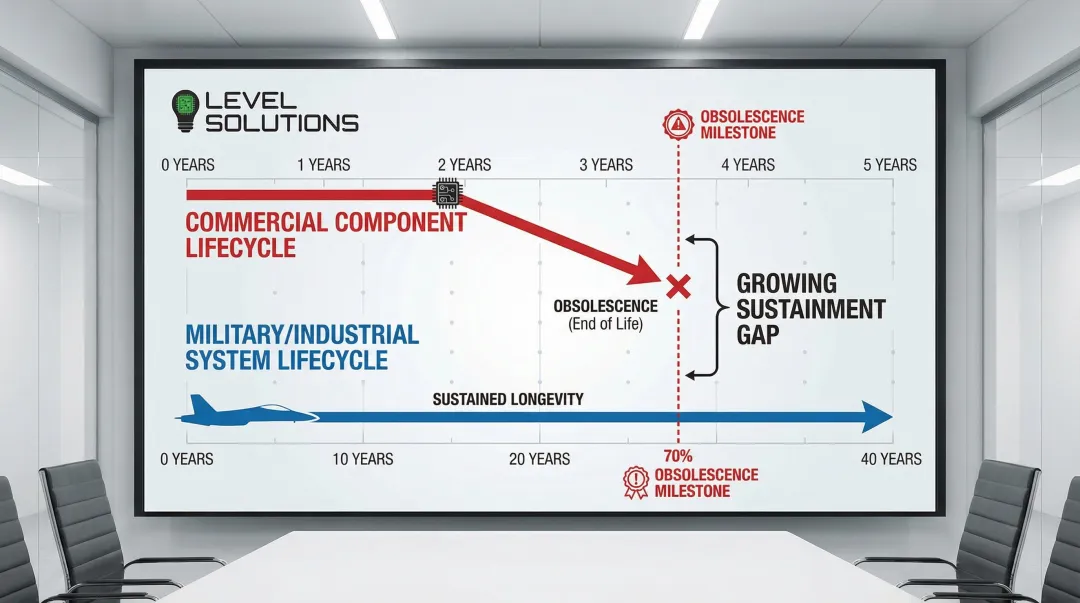
The root cause is a fundamental lifecycle mismatch. Commercial electronic components have average lifecycles of just 2 to 5 years before manufacturers discontinue them for newer designs.
Yet military platforms, medical devices, and industrial systems operate for 20 to 40 years—sometimes exceeding 50 years. This disparity creates a predictable crisis: 70% of electronics procured by the DoD are obsolete prior to system fielding.
Why Obsolescence Matters Across Industries
Military and Defense: Defense platforms like aircraft, ships, and ground vehicles operate for 30-40 years, far exceeding component availability.
When an F-16 fighter jet requires a replacement processor from 1995, sourcing authentic parts becomes mission-critical.
Commercial Sectors: Telecommunications infrastructure, medical imaging equipment, and industrial automation systems face identical challenges. A hospital CT scanner with a 15-year service life depends on components with 3-year production runs.
When failures occur, hospitals can't simply upgrade. Regulatory approvals and capital costs make component-level repair the only viable option.
Financial Impact: Redesigning systems to accommodate newer components costs hundreds of thousands to millions of dollars. Minor redesigns average $111,000, while major redesigns average $410,000. For many organizations, sourcing obsolete parts—even at premium prices—remains more cost-effective than engineering alternatives.
The Scope of the Obsolescence Challenge
The defense electronics obsolescence market was valued at $2.7 billion in 2024 and is projected to reach $6 billion by 2034, growing at 8.4% annually. This growth reflects aging military fleets, extended platform lifecycles, and the accelerating pace of commercial component obsolescence.
Integrated circuits (ICs) dominate obsolescence demand, accounting for 82% of all counterfeit reporting. The most commonly affected components include:
- FPGAs and programmable logic devices
- Memory chips (DRAM, SRAM, Flash)
- Microprocessors and DSPs
- Analog-to-digital converters
- Power management ICs
Manufacturers like Xilinx, Intel, Analog Devices, and Texas Instruments are among the most frequently counterfeited brands, as their high-value components command premium prices in secondary markets.
The Counterfeit Risk in Obsolete Parts Procurement
The obsolete parts market is particularly vulnerable to counterfeiting because limited supply creates high demand and profit margins that attract fraudulent actors. The Semiconductor Industry Association estimates counterfeiting costs U.S.-based semiconductor companies more than $7.5 billion annually, with 82% of counterfeit incidents involving integrated circuits.
Common Counterfeiting Techniques
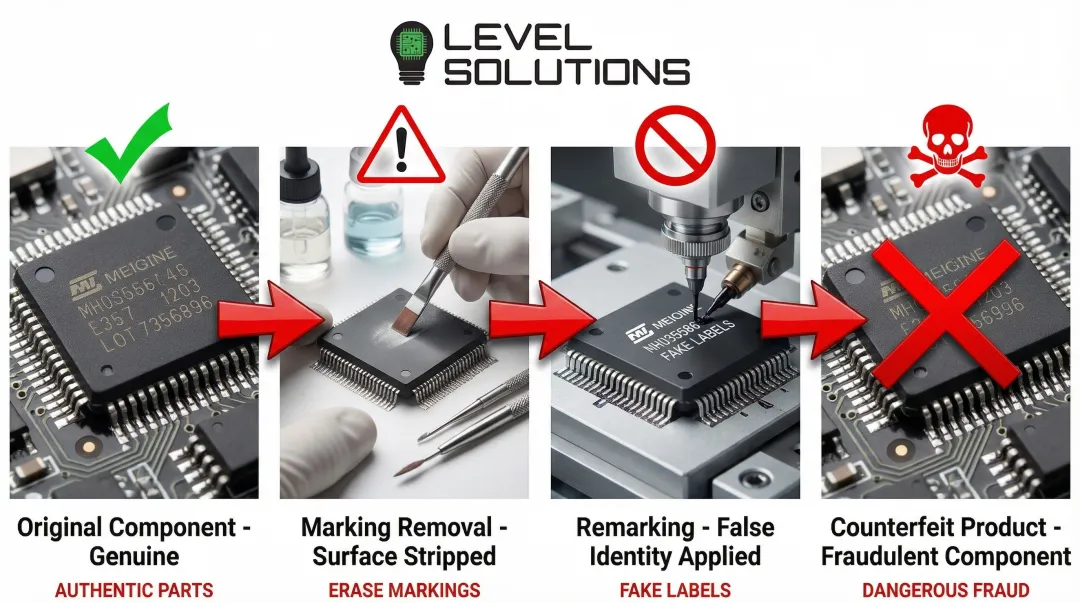
Blacktopping is the most prevalent counterfeiting method. Counterfeiters sand off existing markings on used, discarded, or lower-grade components, then remark them as new or higher-specification parts.
The process typically involves:
- Physically removing original manufacturer markings through sanding or chemical etching
- Applying new markings that misrepresent date codes, lot codes, speed grades, or country of origin
- Remarking commercial-grade parts as military-specification components
- Upgrading speed ratings (e.g., a 1GHz processor remarked as 2GHz)
Many counterfeits aren't complete fakes—they're genuine OEM parts that have been recycled, damaged, downgraded, or misrepresented.
A legitimate Intel processor pulled from e-waste and remarked with a newer date code passes basic visual inspection despite being counterfeit.
Real-World Consequences
A Senate Armed Services Committee investigation in 2012 identified approximately 1,800 cases of suspect counterfeit parts involving over 1 million individual parts in U.S. military systems.
Specific incidents include:
- Navy SH-60B Helicopters used counterfeit electromagnetic interference filters; failure could compromise night missions and missile operations
- Air Force C-27J Aircraft installed suspect counterfeit memory chips in mission-critical systems
- THAAD Missile Defense System incorporated counterfeit devices in mission computers that would likely cause complete missile failure
The "walking wounded" phenomenon describes parts that work sporadically, operate below specification, or fail under stress conditions like temperature extremes or voltage fluctuations.
These failures are unpredictable and severe. A counterfeit component may function perfectly during ground testing but fail during a critical mission.
Why Counterfeits Are Hard to Detect
Visual inspection and basic continuity testing cannot detect remarked genuine parts or performance-grade misrepresentation. A blacktopped component looks authentic under magnification, and a remarked processor will power on and execute basic functions.
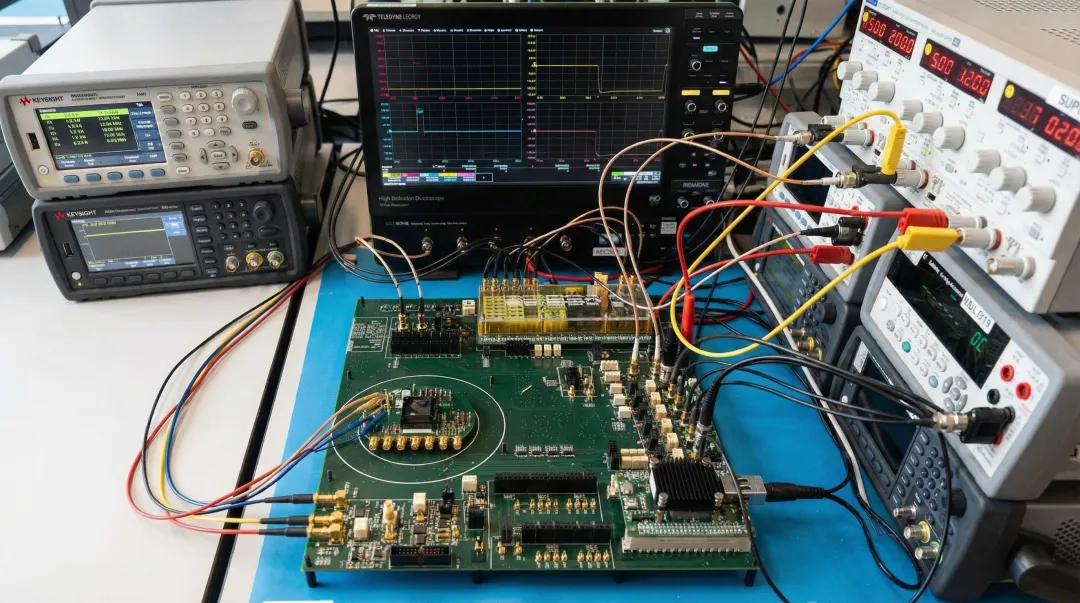
Detecting these counterfeits requires thorough electrical testing using automatic test equipment at full operational parameters.
Testing must verify:
- Speed and timing specifications at rated frequencies
- Voltage and current parameters across full operating ranges
- Temperature performance from -55°C to +125°C (for military components)
- All datasheet specifications, not just basic functionality
High-speed SerDes interfaces and DDR3/DDR4+ memories are particularly vulnerable. Testing requires specialized equipment capable of validating signal integrity at multi-gigabit speeds.
Without proper testing infrastructure, counterfeits go undetected until field failures occur.
Supply Chain Vulnerability Points
Even sophisticated testing can't protect against counterfeits if supply chain vulnerabilities aren't addressed. Counterfeits enter through gray market brokers, overseas suppliers, and multiple reseller layers that obscure component origin.
When parts pass through 3-4 intermediaries before reaching end users, tracing component origin becomes nearly impossible.
Even defense contractors with rigorous quality programs have unknowingly purchased and installed counterfeit components. The challenge isn't incompetence.
It's the sophistication of modern counterfeiting operations that exploit gaps in supply chain visibility.
Key Procurement Strategies for Obsolete Components
Successful obsolescence management requires a multi-layered sourcing strategy rather than relying on a single channel. Each approach has distinct advantages and limitations.
Strategy 1: Authorized Distributors and Franchised Channels
Advantages:
- Direct OEM relationships guarantee authenticity
- Proper storage conditions and ESD-compliant handling
- Full traceability documentation and certificates of conformance
Limitations:Authorized distributor inventory depletes rapidly once parts are discontinued. Manufacturer policies typically allow Last Time Buy (LTB) orders within 6-12 months of the Product Discontinuance Notification (PDN), with final shipments occurring 6-12 months later.
This creates a 1-2 year window before authorized inventory disappears completely.
Recommendation: Establish relationships early and execute lifecycle buys when possible for critical components. Monitor PCNs and EOL announcements proactively rather than reactively.
Strategy 2: OEM Surplus and Excess Inventory Programs
Some manufacturers maintain limited stock of discontinued parts or offer last-time-buy opportunities before completely halting production.
Monitoring Product Change Notifications (PCNs) and End-of-Life (EOL) announcements according to JEDEC standards (J-STD-048 for discontinuance, J-STD-046 for changes) allows you to procure proactively.
Negotiate directly with OEMs for access to remaining inventory or arrange final production runs. While this requires capital investment and storage costs, it secures authentic components with full manufacturer support.
Strategy 3: Specialized Obsolete Parts Distributors
When authorized channels are exhausted, aftermarket distributors fill the gap by specializing in hard-to-find and obsolete components.
LEVEL SOLUTIONS, for example, maintains millions of parts ready for immediate shipment from ESD-compliant warehouses, with access to billions more components globally through established sourcing networks.
What to Look For:
- Global sourcing networks with access to diverse suppliers
- In-house testing capabilities following SAE AS6171 standards
- Proper certifications and transparent supply chain documentation
- ESD-compliant warehouses and component handling procedures
- Coverage of both commercial and military-specification components
LEVEL SOLUTIONS provides comprehensive manufacturer coverage across all major brands including Intel, Texas Instruments, Analog Devices, Microchip Technology, and NXP, with quality standards that exceed industry benchmarks.
Strategy 4: Component Harvesting and Refurbishment
Harvesting components from decommissioned equipment may be appropriate for extremely rare components with no alternative sources. This approach requires:
- Rigorous testing and validation to ensure harvested components meet specifications
- Visual inspection for lead damage, re-tinning, or thermal stress indicators
- Electrical testing at full operational parameters
- Documentation of source equipment and handling procedures
Risks: Harvested components have unknown stress histories and reduced reliability. Use this approach only when no other options exist and accept the elevated failure risk.
Strategy 5: Redesign and Alternative Components
When sourcing costs escalate or reliability concerns mount, redesign becomes more cost-effective than continued obsolete parts procurement. Form-Fit-Function (FFF) replacement strategies identify drop-in alternatives that physically replace obsolete components without requiring board redesign.
Redesign becomes preferable when:
- Obsolete parts exceed 3-5x original pricing
- Reliable sources are no longer available
- Long-term system viability requires modernization
- Extended platform life justifies redesign costs ($111,000 for minor, $410,000 for major)
Balance redesign costs, requalification requirements, and timeline constraints against the total cost of ownership for continued obsolete parts sourcing.

Quality Assurance and Verification Methods
When sourcing obsolete components from non-authorized channels, procurement teams face significant risk. Rigorous testing becomes your only defense against counterfeit or compromised parts.
The SAE AS6171 standard provides a comprehensive testing hierarchy that reputable suppliers follow:
| Test Method | Purpose | Detects |
|---|---|---|
| External Visual Inspection | First-line screening | Sanding marks, remarking, lead damage, package inconsistencies |
| X-Ray Analysis | Internal structure verification | Die size, wire bond integrity, internal construction anomalies |
| X-Ray Fluorescence (XRF) | Material composition | Lead finish composition, re-tinning, RoHS compliance issues |
| Decapsulation | Die verification (destructive) | Manufacturer logos, part numbers, copyright dates on silicon |
| Acoustic Microscopy | Internal defect detection | Delamination, cracks, voids indicating prior use or damage |
| Electrical Testing | Functional verification | Performance at full operational parameters, temperature extremes, voltage ranges |
Implementing Electrical Testing Protocols
Electrical testing at full operational parameters (speed, temperature, voltage) should verify all datasheet specifications. Basic functionality checks aren't enough.
Military components require testing across -55°C to +125°C temperature ranges. This reveals commercial parts fraudulently remarked as military-grade, a common counterfeit tactic.
Critical testing checkpoints include:
- Full datasheet specification verification, not just pass/fail functionality
- Stress testing at voltage and temperature extremes
- High-speed signal integrity for logic and memory components
- Parametric testing for analog devices (offset voltage, gain, linearity)
Suppliers with quality programs exceeding industry standards typically implement multiple test layers. LEVEL SOLUTIONS' ESD compliant warehouse, for example, ensures components remain protected throughout the verification and fulfillment process, preserving test integrity from receipt through shipment.
Working with Specialized Distributors
When components go obsolete, specialized distributors become critical supply chain partners. The right partner reduces procurement risks through proven expertise, global sourcing networks, and rigorous quality assurance.
Key qualifications to evaluate include:
Comprehensive Inventory Access:
- Millions of components stocked for immediate availability
- Global sourcing networks accessing billions of parts worldwide
- Coverage of both commercial and mil-spec components
Quality Standards:
- Rigorous testing protocols following SAE AS6171
- ESD-compliant warehousing and handling procedures
- Full traceability documentation with certificates of conformance
Manufacturer Coverage
Look for distributors with broad manufacturer relationships. LEVEL SOLUTIONS, for example, maintains coverage across all major semiconductor manufacturers including Xilinx, Intel, Analog Devices, Texas Instruments, Microchip Technology, NXP, Infineon, and Motorola.
Their ESD-compliant warehouses stock millions of parts for immediate shipment. When local inventory doesn't meet requirements, global sourcing networks provide access to billions of additional components worldwide.
Best Practices for Long-Term Obsolescence Management
Effective obsolescence management requires a systematic approach combining proactive monitoring, rigorous documentation, and strategic purchasing. These three pillars work together to minimize supply chain disruptions and ensure long-term product supportability.
Proactive Obsolescence Management Program
- Monitor component lifecycles using automated tools tracking PCNs and EOL notices to receive advance warning of discontinuations
- Maintain Approved Vendor Lists (AVLs) with multiple qualified sources
- Create obsolescence risk assessments for critical systems using DMSMS (Diminishing Manufacturing Sources and Material Shortages) methodologies that identify at-risk components before supply issues emerge
- Implement lifecycle forecasting to predict obsolescence before it occurs
Comprehensive documentation protects against counterfeit parts and ensures traceability throughout your supply chain.
Documentation Requirements
- Full traceability with certificates of conformance
- Test reports validating electrical specifications at operational parameters
- Chain of custody documentation from OEM through all distributors
- Country of origin verification for compliance and authenticity
- Supplier declarations of authenticity for non-authorized sources
When components approach end-of-life, strategic lifetime buys can secure your supply for years to come.
Lifecycle Buy Strategies
- Calculate lifetime part requirements based on failure rates and platform service life
- Negotiate volume purchases before EOL to secure pricing and availability
- Balance inventory carrying costs against future scarcity and price increases
- Establish secure, climate-controlled storage with ESD protection
Conclusion
Successful obsolete parts procurement balances authenticity, reliability, and mission-critical performance with strategic cost management. The cheapest component rarely delivers the best value when counterfeit risks and system failures enter the equation.
The counterfeit threat continues to grow, with 15% of Pentagon spare parts estimated to be counterfeit and billions in annual costs to the semiconductor industry. A resilient procurement strategy requires multiple layers of protection:
- Combine authorized sources with vetted specialized distributors
- Implement rigorous quality verification at every step
- Integrate lifecycle management into product design and supply chain planning
- Build relationships with suppliers offering comprehensive sourcing capabilities
Organizations that treat obsolescence as an ongoing strategic process—not a crisis to solve when parts fail—maintain operational continuity. Access to extensive inventory networks, both local and global, provides the flexibility to source critical components before they become procurement emergencies.
Frequently Asked Questions
What are counterfeit electronic components?
Counterfeit components are parts misrepresented regarding origin, grade, or condition—including fake parts, remarked genuine parts, recycled components sold as new, and altered date codes or performance ratings.
How can you identify counterfeit electronic components?
Identification requires visual examination for marking inconsistencies, X-ray analysis for internal structure, and electrical testing at full operational parameters to verify all datasheet specifications.
What are the main challenges in procuring obsolete electronic parts?
Key challenges include limited availability (authorized inventory depletes within 1-2 years post-EOL), high counterfeit risk (15% in defense supply chains), price volatility, and difficulty verifying authenticity through gray market channels.
How do you verify the authenticity of obsolete components?
Source from reputable distributors with SAE AS6171-compliant testing capabilities, require full traceability documentation to the OEM, and conduct electrical testing validating all datasheet parameters—not just basic functionality.
What documentation should you require when purchasing obsolete parts?
Essential documentation includes certificates of conformance, test reports verifying electrical specifications, chain of custody tracing to the OEM, country of origin certificates, and supplier authenticity declarations.
When should you consider redesigning vs. sourcing obsolete parts?
Redesign becomes preferable when parts are unavailable from reliable sources, costs exceed 3-5x original pricing, or long-term viability requires modernization. Balance this against redesign costs ($111K-$410K), requalification requirements, and timeline constraints.